What is a networked safe lock?
A networked safe lock solution gives you more control over locks in multiple locations, including centralized, remote access. With remote access safe locks, you can streamline management and operation from one central location, including the ability to remotely:
- Monitor live lock status
- Manage user codes
- Program lock settings
- Enable/disable locks
- Establish different levels of access
- Create available access windows
- Receive exception reporting
- Perform audits
How do you choose the best networked safe lock?
When choosing a networked safe lock, or helping a customer find the right product, it helps to start with a decision framework. Regardless of where you are in the process, our simple framework helps you define requirements and assess critical factors like compatibility, security, and maintenance costs, making it easier for you to select the right product for your needs. We’ll walk you through helpful information at each step, with additional resources for those who need more detailed research.
- DEFINE REMOTE ACCESS REQUIREMENTS
- ESTABLISH COMPATIBILITY
- EVALUATE CONNECTION SECURITY
- WEIGH ONGOING MAINTENANCE COSTS
- CONSIDER A UNIQUE DIGITAL PLATFORM SOLUTION
- RECAP AND EVALUATE
Find out if a Networked Safe Lock is right for you.
Get more details about networked safe locks, including specifications and customization options.
1. Define remote access requirements
To choose the right access solution for multiple safes, start by defining your needs.
Lay Groundwork
- How many safes and locations do you need to secure?
- Do you plan to scale up to more locations over time?
- Do you need remote access and management, or prefer to handle access control at each lock?
- Do you need a centralized locking system, or prefer each lock to stand alone?
- How many people will access each safe? Do those users require different levels of access, such as owner, admin, or specialized functions?
- How would you prefer to receive reporting about access issues?
Survey Locations
- Will you be upgrading existing electronic safe locks, replacing mechanical locks with new electronic units, or adding incremental units for new or expanded locations?
- Is the area already part of an existing IP network?
- Is there Wi-Fi? What security protocols are in place for that network?
- Do you have capacity/capability to perform complex retrofit tasks like drilling and wiring?
Establish Budget Parameters
- Does the scale of your network support adding a separate hub component to network the locks?
- How much maintenance budget can you build in to support the system?
- Is extensive installation/retrofit possible within the budget?
- Will the solutions you consider come with any offset costs? For example, reduced downtime, reduced risk, or longer product life may serve to balance the cost of the initial investment.
What’s the most cost-effective Networked Safe Lock?
Learn how to control multiple access points remotely (and cost-effectively).
2. Establish Compatibility
IP lock installation requirements vary in complexity. In addition to drilling and wiring, some locks require an additional hub component to manage network connectivity and may also require frequent battery changes for operation. Before you purchase new locks, be sure to consider:
Power Options
- Does the lock offer external power, or run from battery power?
- How easy are the batteries to change?
- What back up options exist to prevent the system from going down when batteries run down or power goes out?
Installation Requirements
- Does the lock require drilling to install or retrofit?
- If you’re replacing existing locks, will the new locks fit into the old footprint, or will a more complicated retrofit process be required?
- If the system requires peripheral components, how and where will they be installed?
- What additional tools are required to install or retrofit the lock?
Not all IP Locks are difficult to install.
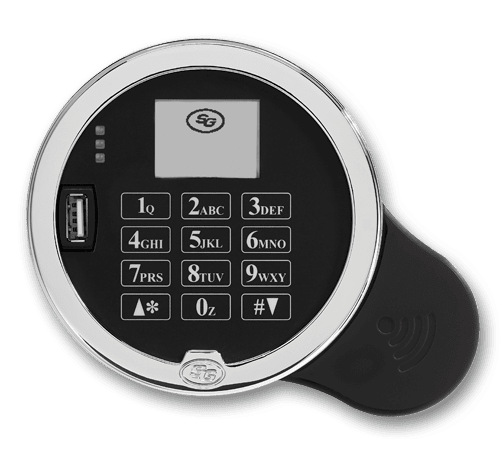
For example, the Sargent and Greenleaf NexusIP™ lock simplifies installation by using a standard footprint and routing through existing wiring and networks.
3. Evaluate connection security
When you use networked safe locks, your security is only as strong as the network supporting your solution. Lock manufacturers support connectivity in two main ways:
Extra Components
In many cases, IP locks route through an external hub component. When considering these models, think about:
- How much the hub will add to the cost of your network.
- How the hub will be installed and powered.
- What backup programs are in place to support the locks if the hub goes down or loses power?
- The security standards of the hub design—particularly if those protocols satisfy your organization’s requirements.
Wi-Fi Networking
The latest IP lock breakthroughs include Wi-Fi networking. Using a local Wi-Fi connection, these locks don’t require purchasing peripheral components, are simpler to install, and easier to maintain. But are Wi-Fi safe locks secure?
- When paired with a secured Wi-Fi network—using firewalls and secure VPN, for instance—Wi-Fi safe locks are secure.
- Many users cloak the devices within the secured network for additional security.
- If Wi-Fi connections are lost, Wi-Fi networked locks still function securely through the keypads. Once the network is restored, connectivity and audit events synchronize wirelessly.
- Check the security standards of devices you consider. For example, the Sargent and Greenleaf NexusIP meets industry encryption standards through proprietary security features build into the device.
WiFi for Networked Safe Locks? Seriously?
Top security myths unpacked: why Wi-Fi keeps your safes more secure.
4. Weigh ongoing maintenance costs
Part of determining the overall cost of a networked safe lock solution comes down to maintenance. Planning ahead for maintenance ensures that your system functions smoothly, while also staying within your budget. Maintenance costs for networked safe locks generally involve components, power supply, and downtime.
Components
It stands to reason: the more components associated with your system, the more time it takes to keep them in good working order. Be sure you factor in peripheral components like network hubs in addition to the locks themselves.
Power Supply
Relying on battery power means that many IP locks need frequent maintenance time to travel to the lock and change the batteries. This task should be performed on a regular basis to prevent loss of power. On the other hand, locks that rely on external power with batteries for backup take less time to service.
Downtime
Each time a lock or component requires service, your network experiences downtime. To reduce the costs associated with planned and unplanned downtime, consider lock systems that use external power. Locks with an external power source deliver dependable, ongoing operation, without frequent service or downtime.
Looking for ways to reduce maintenance and downtime?
How to keep remote access safe locks online and running smoothly.
5. Consider a unique digital platform solution
Organizations of all sizes often wonder how to reduce complexity in networked access control. When the engineers at Sargent and Greenleaf worked on that problem, they identified multiple opportunities for streamlining without sacrificing security. In this example, we’ll consider the Sargent and Greenleaf Nexus IP lock, but, as with the balance of the framework, these criteria could be applied to other products as well.
Leverage Existing Technology
Hub components are often sold as being necessary for security. Our engineers found that modern security standards fully mitigated the network risks of the past. That’s why NexusIP simplifies networked safe locks—all you need is NexusIP and your existing secure Wi-Fi.
Streamline Management and Operation
By using your existing Wi-Fi network, NexusIP allows users to easily program networked locks via software interface, so you can establish multiple levels of control, program schedules, and user access, as well as operate the lock and review audit trails and real-time updates from one central, secure point.
Simplify Installation
Built to the Sargent and Greenleaf Magic Module specifications, NexusIP fits the standard footprint of most safe locks. And because you won’t need to wire into Ethernet or a peripheral hub, no drilling or additional tools are required.
Make It Scalable
As a scalable solution, NexusIP works for organizations of all sizes. While it presents a dramatic value for large-scale organizations, NexusIP is also ideal for smaller businesses with fewer units—because removing the hub requirement makes a networked locking system more affordable. Regardless of business size, NexusIP easily scales as your company grows. Manage up to 100 users and check up to 1,000 audit events at the lock, while viewing and storing unlimited events remotely via our software interface.
Keep It Updated
The Sargent and Greenleaf Digital Platform integrates the latest technology breakthroughs with the highest standards for security. Designed for future-proof flexibility and advanced data management, our Digital Platform products—including NexusIP—help your organization and security evolve to meet changing environments.
Need to see the specifics?
Download detailed information about the Sargent and Greenleaf NexusIP networked safe lock.
6. Recap and evaluate
Organizations of all sizes often wonder how to reduce complexity in networked access control. When the engineers at S&G worked on that problem, they identified multiple opportunities for streamlining without sacrificing security. In this example, we’ll consider the Sargent and Greenleaf Nexus IP lock, but, as with the balance of the framework, these criteria could be applied to other products as well.
About Sargent and Greenleaf
For more than 160 years, S&G has made governments, banks, and businesses more secure. Now a global company headquartered in the U.S., we continue to deliver leading-edge innovation. Our award-winning solutions set industry standards and have earned the trust of customers worldwide. Sargent and Greenleaf balances technological advances with proven security in seamlessly integrated designs.

